TOR Website Redesign
As part of an effort to get involved in open-source experience design, I thought I would lend my services to an organization that does amazing work for communities around the world, Tor.
How might we grow Tor’s Usage and gain more public support?
Tor has, in the past, relied heavily on government funding to keep the organization operational. One of their main goals is to move toward more support from the public and not-for-profit organizations. They have, in the last 2 years gone from nearly 90% government funding to around 70%.
Public interest in Tor has been declining but interest in personal security and data protection has been gaining ground.
Tor is missing an opportunity to capture and retain those people that would most benefit from the service that it offers.
As of the day I started out on this endeavor, the Tor website looked like this:
The Plan & My Goals
The current website for the Tor Project is very outdated, technically written - geared too much towards those with technical experience, and disorganized to the point of confusion.
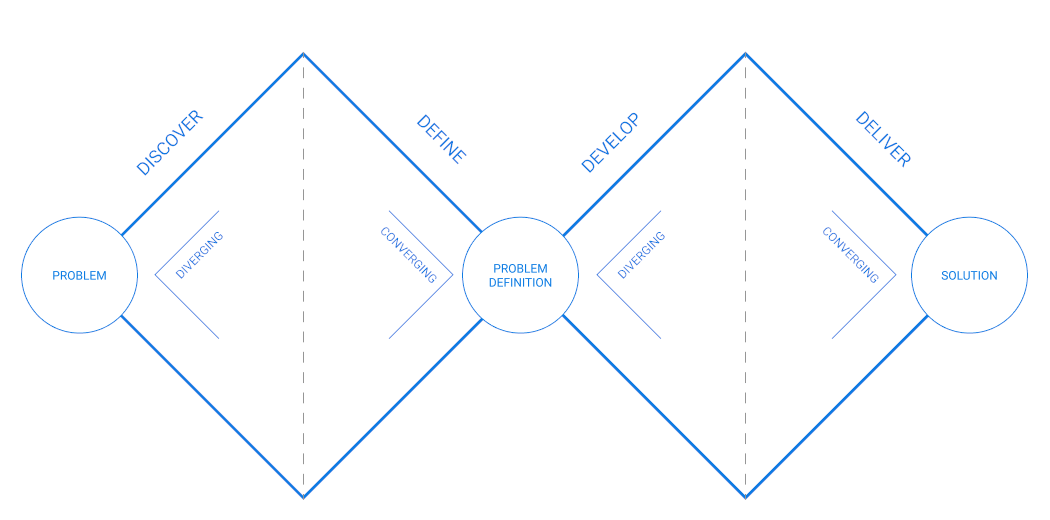
Using an iterative design process, it was my goal to uncover how the site could be realigned to more closely match the organization’s goals, provide clearer information to new users, but also cater the site to those who would be willing to integrate Tor into other projects or help support the network.
Because of the breadth of the Tor ecosystem and the abundance of products and technology that go into supporting the network, I chose to concentrate the discovery and potential solution on the main Tor Project Website since it should be the first place people may end up for information on the network.
Experience Audit
To become more intimately familiar with the site, its information, and its organization, I documented the assumptions I had about users of the site and what task they were looking to accomplish. This would help me identify where I believe the site is lacking and, eventually through customer interviews, validate the assumptions and determine the impact to users.
Assumptions
Types of people that would use the site
People who don’t want to be tracked and profiled by Marketing, Data Analytics Firms, or governmental authorities. People that want to integrate the Tor Network into other technologies.
What would visitors want to accomplish?
- Install the tools to help to be able to communicate anonymously online
- Get involved in the development of a Tor Product
- Contribute to the ‘health’ of the network
- Donate money / time
- Learn about what it takes to stay private and secure online
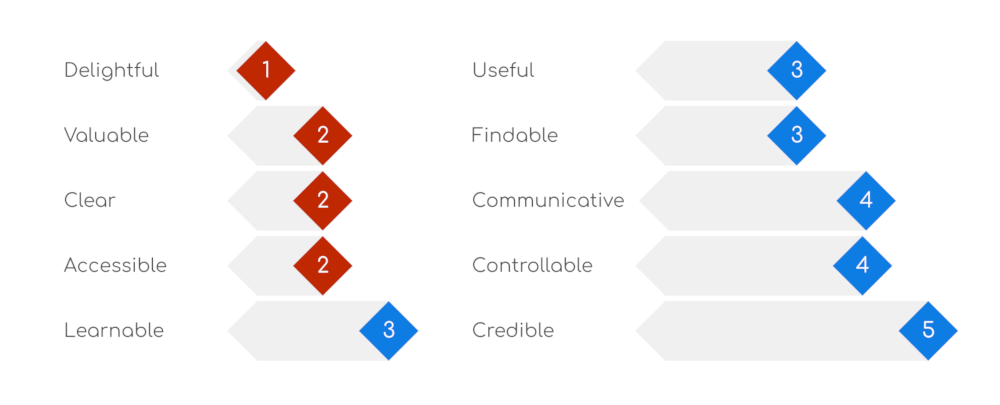
Heuristic Evaluation
I personally find a heuristic evaluation to be very helpful in looking at the experience as a whole and to also identify the good parts of the site - something that I can often overlook when identifying issues.
In the case of the Tor website, there is a lot of information at a high level, but often written to a very technical audience and disorganized to the point of confusion. Trying to find a particular piece of information can often send you to different sites or sections that seem quite unrelated.
Key Findings
In general the Tor website and software does well at:
- Helping people get up and running with the software
- Educating users on how to continually stay anonymous online
However, The Tor Project website:
- Is not representative of the Tor brand
- Has vastly inconsistent designs between each of its products
- Content has become unorganized and has outgrown its original architecture
The Tor Project is likely missing out on opportunities to grow the ecosystem.
Competitive Landscape
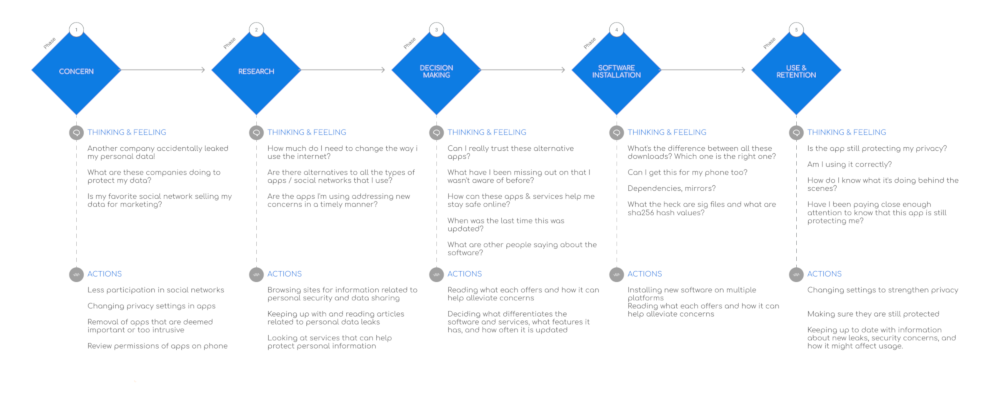
Experience Map
In order to understand the typical process a user would go through when considering Tor, I created an experience map to highlight users thoughts and actions into 5 main phases.
- Concern (Over current privacy and internet usage)
- Research (Around what’s out there and how to be protected)
- Decision Making (Which apps are the best for a user)
- Software Installation (How easy is it to get started)
- Use & Retention (How users interact with the product and what motivates them to continue its use)
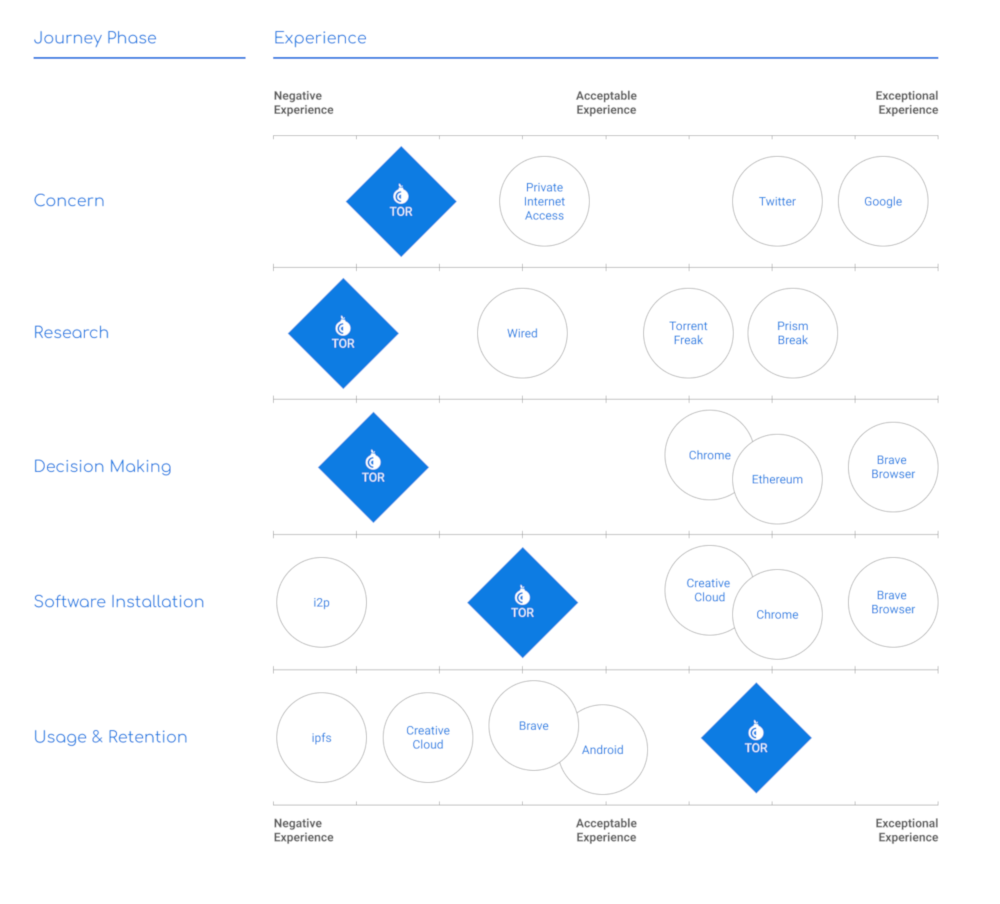
Landscape Analysis
To understand where other innovative experiences exist - I examined several different applications or services both inside and outside of security space in order to understand the extent of these experiences, what services offer a great user experience, and potential opportunities and key takeaways there are to consider for the Tor Project website.
This is how Tor compared to a number of different experiences.
It was clear there was plenty of opportunity for improvement and areas where it can stay ahead of other products.
User Research
I identified several specific opportunities during the experience landscape analysis, the general messaging, how it can support the users’ decision-making process, and how to retain users. I set out to conduct user interviews to confirm and validate those opportunities.
I was looking to potentially uncover more areas of opportunity and help determine the importance placed on them by users of the Tor Project website.
Research Goals
Based on the 5 areas identified in the experience landscape, I devised a set of questions focused on:
- Validating user’s concerns regarding security, privacy.
- Uncovering the personal motivations in choosing Tor over other available products/networks.
- Confirming the main phases of the user experience, from an interest in personal security to using and contributing to the Tor network.
- Identify new opportunities.
- Getting a clear understanding of users’ behaviors.
- Developing clearer, more appropriate messaging around the Tor Brand based on the understanding of its users.
- Prioritizing opportunities.
Participants
I was able to get a broad range of participants with differing levels of knowledge of the Tor network, familiarity with the Tor Project website, and variance in their motivations to participate in their use.
These included:
- A Technical Program Manager with an understanding of networking who uses Tor personally to keep his web browsing anonymous.
- A Social Media Manager a cryptocurrency that uses the Tor Network for mixing making the currency untraceable to an origin.
- A Content Strategist for an Online Lottery and Gambling company who uses Tor in his job to research future competitors and personally to tap into knowledge that isn’t shared to the general web.
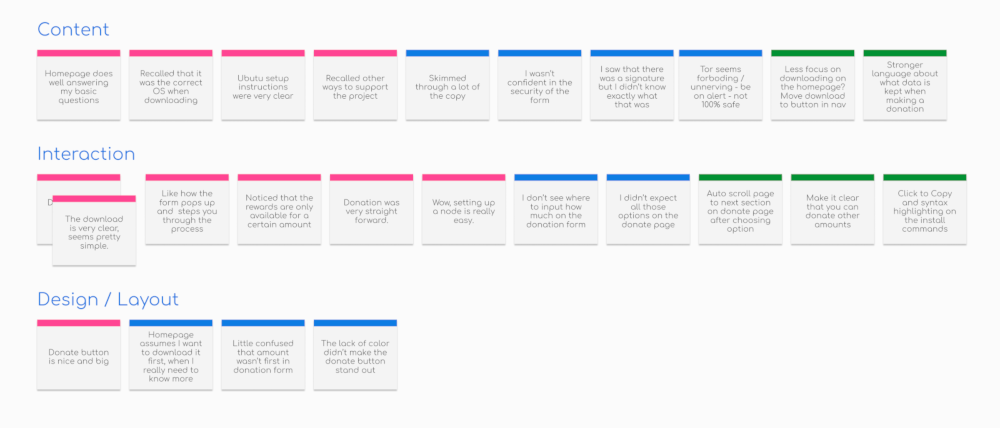
Research Findings
Each participant brought a unique understanding and perspective from their own experiences. Their feedback clearly showed that their expectations of the Tor project website was lacking and there was plenty of opportunity to be addressed going forward.
The current website is not reflective of the user’s expectations or needs.
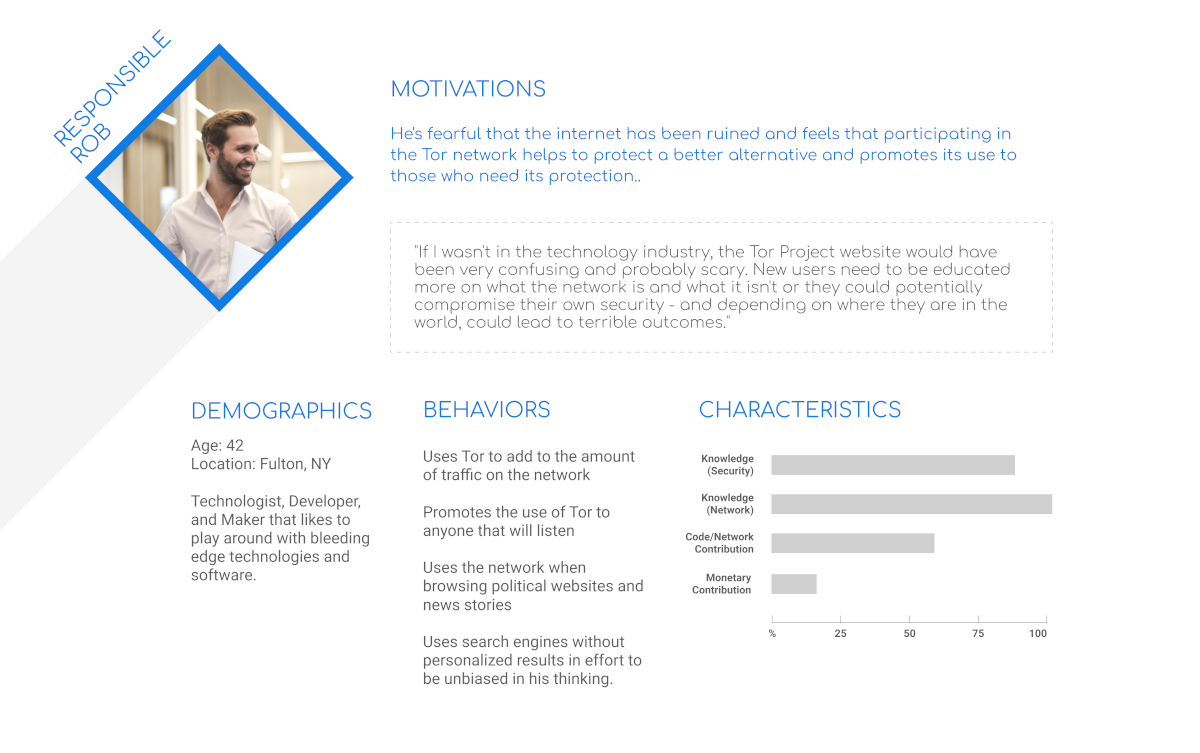
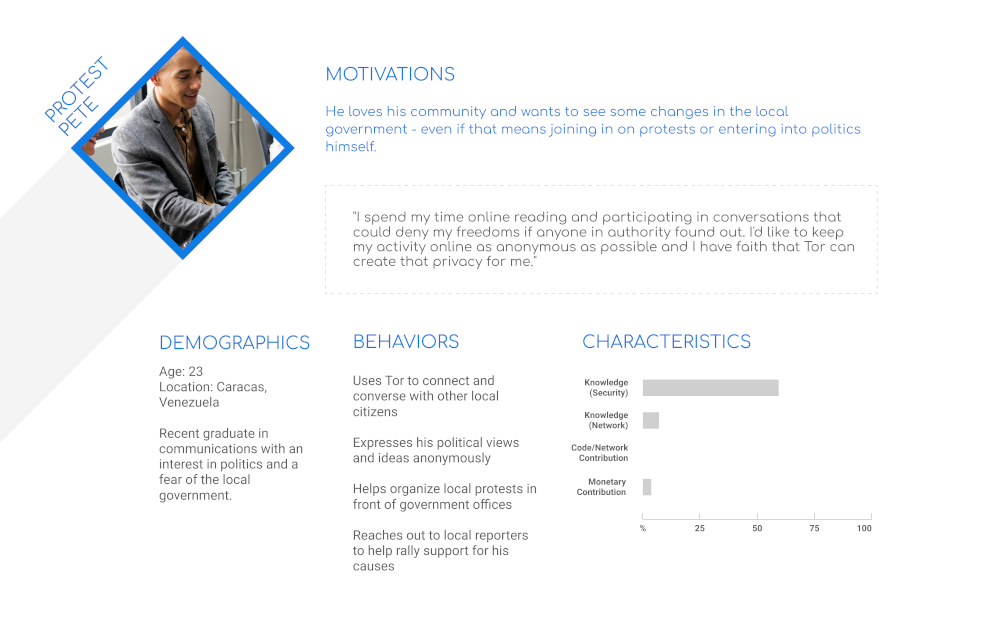
Persona Development
The findings from the participants were synthesized into two personas that covered a broad range of motivations, behaviors and characteristics of Tor’s user base. I kept these close at hand as I moved through the rest of the process, always making sure I had these users in mind.
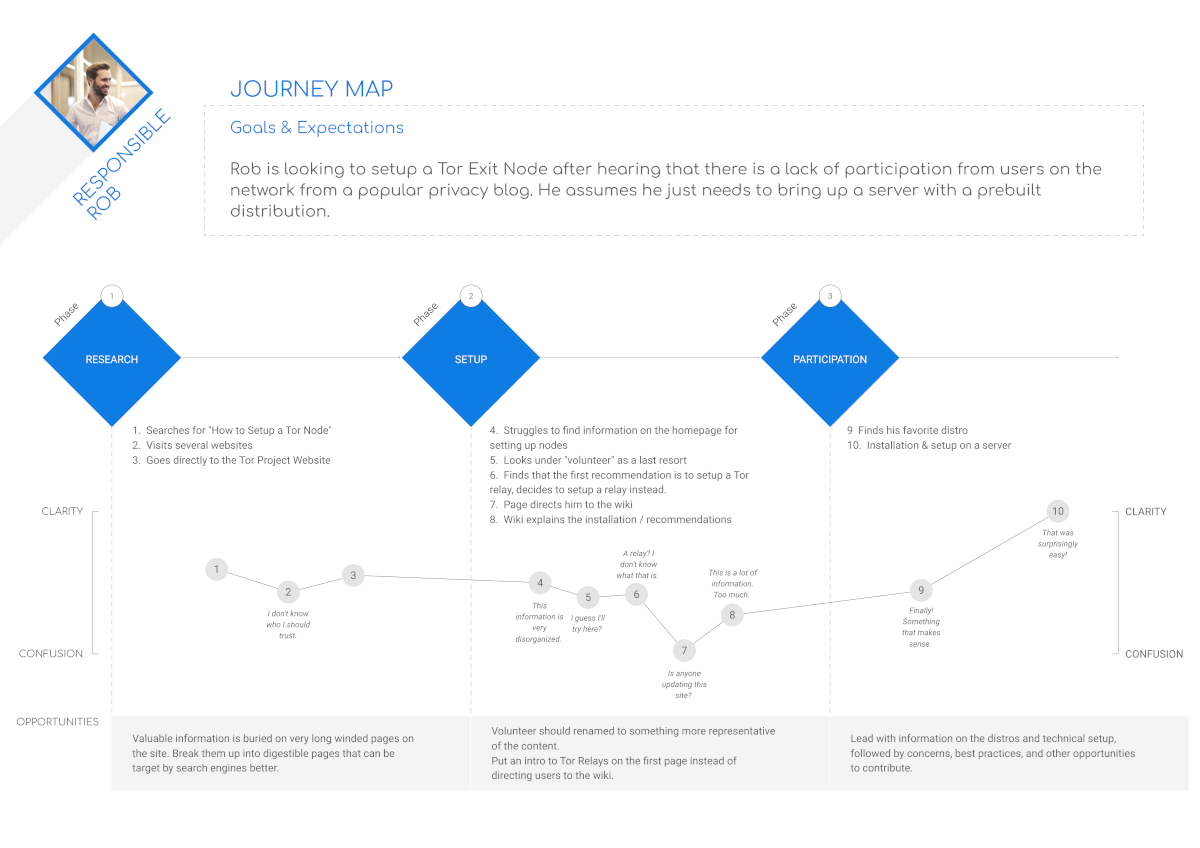
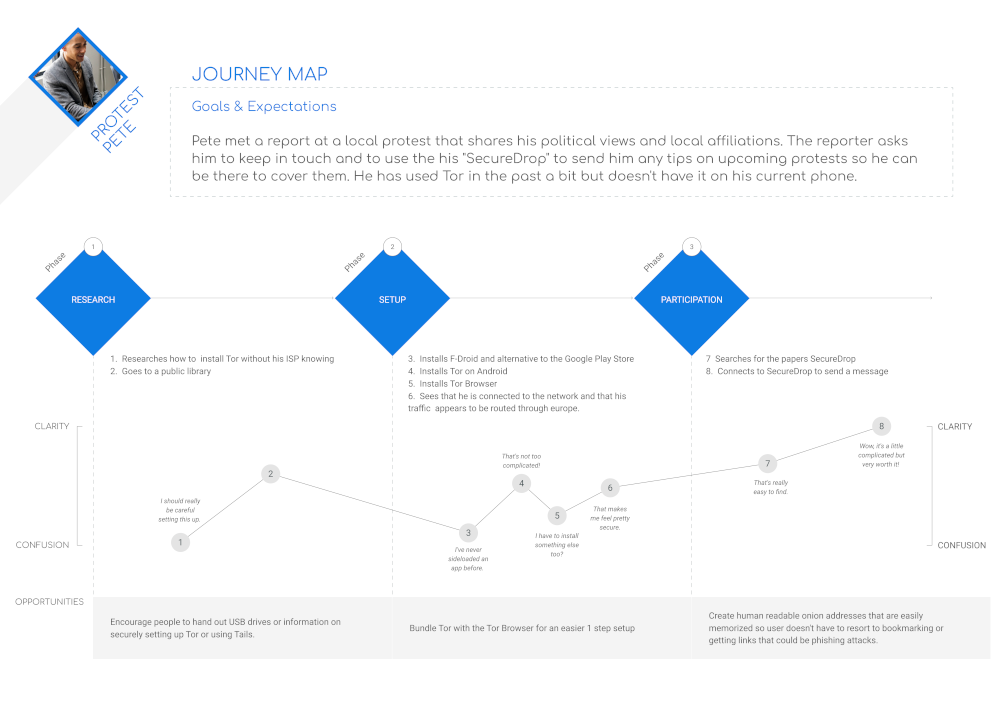
Journey Maps
To get a clearer understanding of where, during the processes, the site expectations were not met. I took the two personas and created customer journey maps to detail their experiences and to identify any potential for improvement.
Though each of the experiences end on a positive note there was plenty during the process that could be improved on.
From Discovery to Design
Moving beyond the discovery phase and into design, the first opportunity I wanted to explore was combining each of Tors’ disparate site properties into a single experience and how that could be addressed in a new architecture. The site was clearly built up over time to include many new areas of content and multiple tools without an overall consideration for how it would affect its usefulness.
Information Architecture
Aside from combining each of the tools together into a single site, many of the user flows I used during my key findings showed how overly complicated the process was for finding information that should be readily available to visitors.
Card Sorting
In order to address what I found most difficult in the architecture of the site, I recruited 3 participants in a card sorting activity. Very quickly users showed a similar mental model of the information - that which was vastly different from how it was presented on the current site.
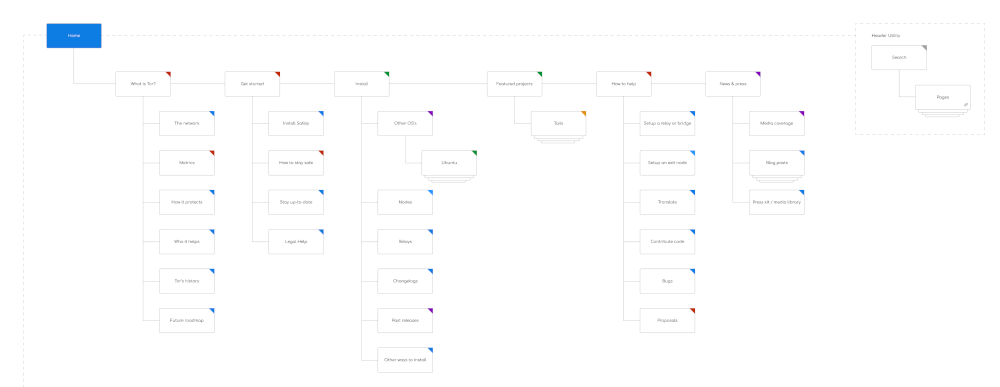
Sitemap
Taking the card sort findings into account I devised a new site architecture that I felt best addressed the user’s needs and potential flows.
Architecture Testing & Iteration
Because of the extent of information contained on the site, I could only use a sampling of content for the card sorting activities. In order to validate what I’d come up with for a full sitemap, I created a TreeJack test and recruited a half dozen participants.
The tests identified some confusion in the semantics of the labeling and how two particular areas of similar content seemed disconnected.
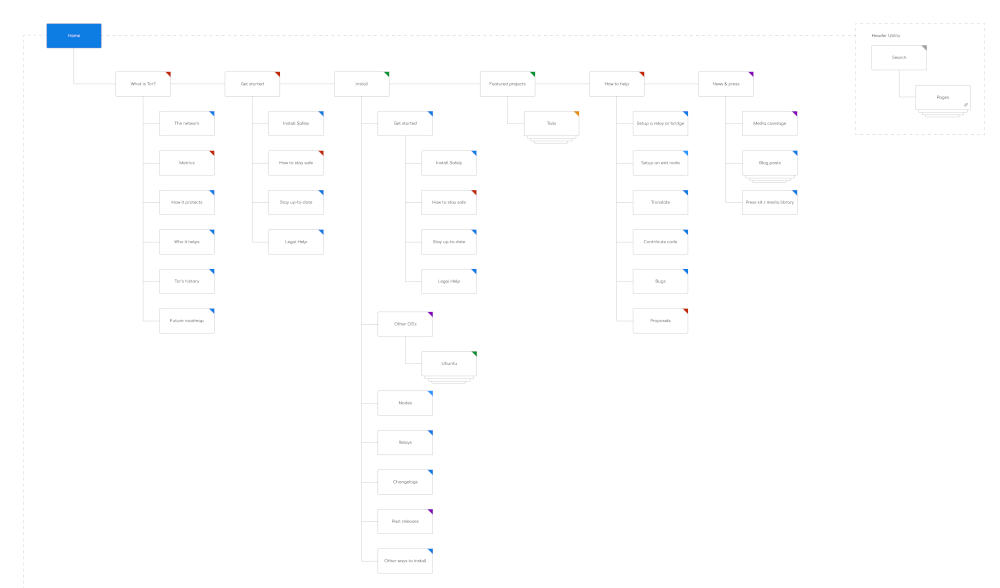
Recommended Architecture & the New User Flows
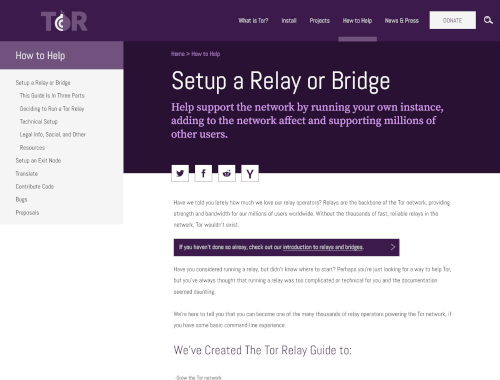
Given the results of the TreeJack testing, I combined two major categories together to be more focused on both educating new users and serving experienced users at the same time. The site’s content is divided into 5 main categories of content that are more easily distinguishable from each other, combine several major products, and create less steps in many of the user flows.
With this new site structure, nearly all the user’s goals are shortened.
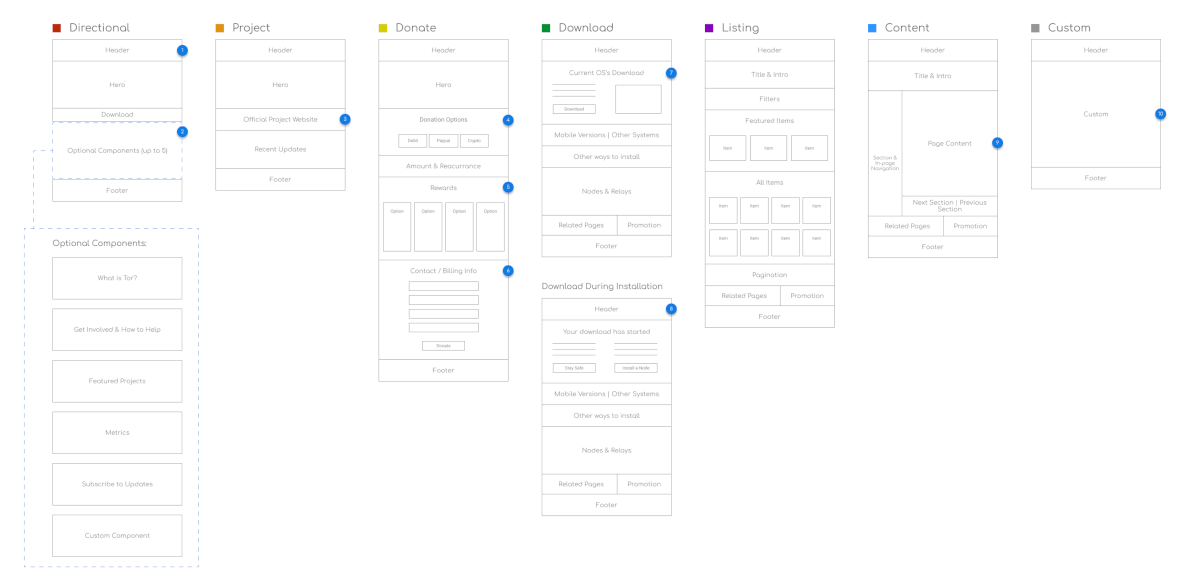
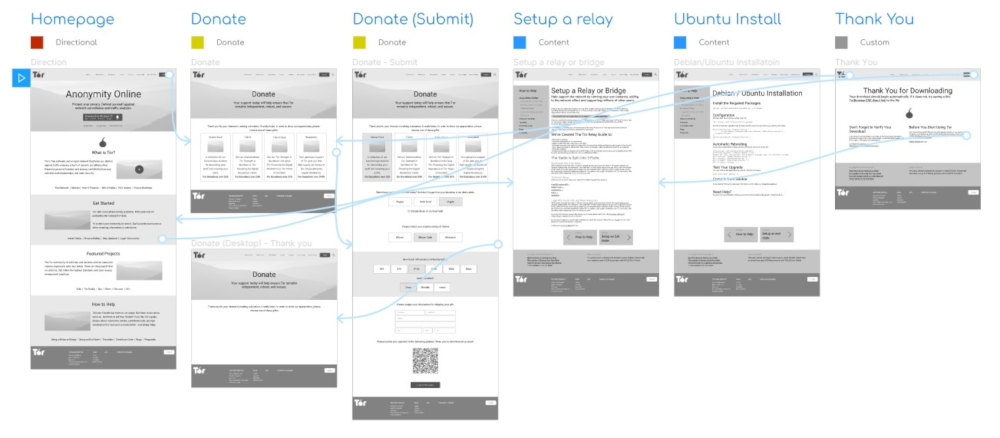
Wireframing & Prototyping
Content Hierarchies
The Tor website is very content-oriented, so identifying component parts of the pages was important for scaling a design solution. All of the content types and presentation of information could be well served by just 6 different general templates and under 20 various components.
Low Fidelity Prototype Testing & Iteration
To be able to gather early, valuable feedback from users I moved into creating low fidelity prototypes - enough to convey the new architecture, new messaging and several of the new user flows.
I conducted 3 in-person usability tests, giving each user 3 tasks to perform from the new user flows:
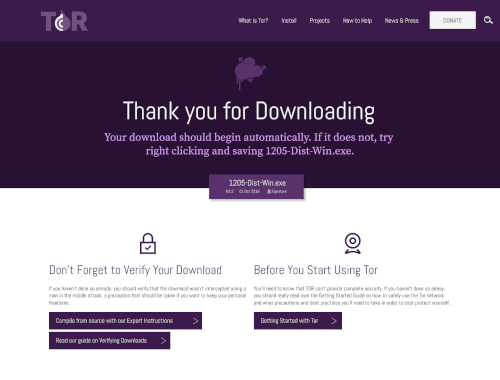
- Install the software for your current system
- Make a $100 donation to the Tor Project using Bitcoin
- Find the instructions for setting up a Tor Relay on an Ubuntu Server
I also conducted a remote test of the new architecture to validate the second round of changes to the information architecture that combined two major categories.
Although each user was able to successfully complete each of the tasks, the donation process could be simplified to be more efficient and clear - which I adjusted in the high-fidelity designs and prototype.
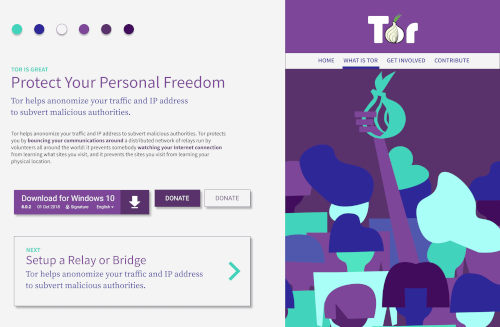
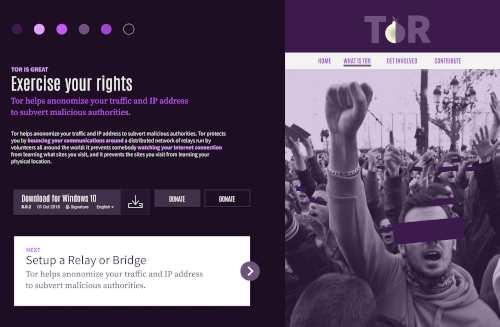
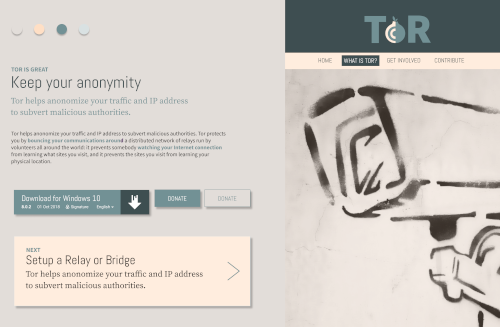
Visual Design
Style Tiles
Tor has established a unique brand and offers a very distinct service with little competition in the space. In several of its products it has adopted a style that differs from the main Tor Project website - a gradual adjustment over the last 10 years.
I wanted to explore a design that would be more representative of what Tor stands for, yet still keeping some aspects of its visual design.
I came up with 3 Mood Board/Style Tiles that took into account some of the components of the site and varying messaging. Eventually considering the 2nd one below for further iterations.
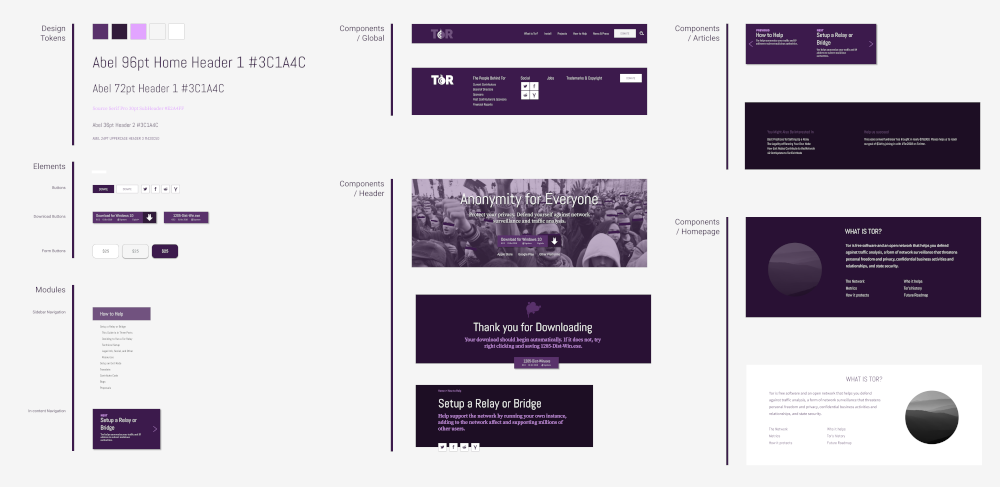
UI Kit
Based on the content hierarchies and components that I identified, I put together a Design System that could easily scale to their existing products beyond the public-facing website.
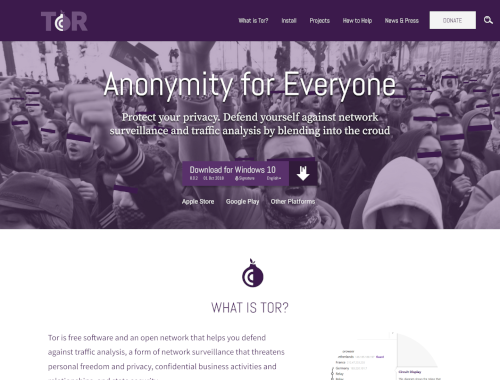
Hi Fidelity Prototypes & Iteration
Combining the UI Kit and Low Fidelity Prototype I was able to test and iterate over a High Fidelity Prototype that, in the end:
- Creates a more streamlined experience for user tasks.
- Displays clearer messaging and intent of the product.
- Organizes content to be more readily available and clear.
- Encourages more volunteer contributions and offers up more ways to help.
- Focuses more on potential user base.
Blend into the Crowd
Everyone’s personal information and security is important, yet there are few products that can offer real anonymity on the internet. More and more companies are harvesting vast amounts of personal information with the intent to sell products, serve up ‘relevant’ information, and make a profit selling that information to others.
If your personal information isn’t already being used for malicious intent, it soon will be.
We need people to help grow the network by donating computer resources. We need developers to keep the network safe by contributing code and bug fixes. We need companies to integrate Tor into their services. And we need everyone to use the network and help grow the crowd.
This new redesign will help align Tor’s organizational goals with user’s expectations and create a more unique and valuable online presence.